We may earn a commission if you make a purchase through the links on our website.
The Best USB Lockdown Software Tools

UPDATED: May 4, 2023
Lock down USB access to your network with this selection of USB access control and DLP solutions.
To allow users to take their flash drives home, network administrators must constantly balance preventing important data loss against USB-based malware. Removable hardware has always posed a threat to the security of your internal network. You can no longer rely on such devices' security when they return to your network after leaving it. Because USB flash drives are one of the main sources of these risks, the simplest approach is to lock down USB access on your network.
You can accomplish this in a variety of ways, but one of the simplest methods is by using USB control software. You can use this software to block unregistered USB external drives and lock down port access.
These software options come in several different packages discussed below. Broadly speaking, there are several freeware options available that can fulfill the task of USB lockdown, but if you’re working in a larger-scale business you may want something more reliable—fortunately, there are centrally controlled DLP (Data Loss Prevention) software solutions that come with USB lockdown functionality as standard.
Here is our list of the best USB lockdown software tools:
- ManageEngine Device Control Plus – EDITOR'S CHOICE You can track and lock down USB access across your network using ManageEngine's Device Control Plus, a full DLP software solution—identify harmful malware and prevent it from accessing your sensitive data by monitoring network activity between your endpoints' USB flash drives. Download the 30-day free trial.
- Endpoint Protector A cross-platform solution by CoSoSys protects your network from malicious USB firmware-based assaults at every endpoint.
- Drivelock Proves itself as an exceptional endpoint protection solution by utilizing both the drivelock USB lockdown features and the built-in encryption and antivirus system, which shields your network from malware and data loss.
- Symantec DLP A comprehensive data loss prevention (DLP) solution that incorporates endpoint monitoring, extensive compliance reporting, and USB lockdown as part of its feature-rich toolbox.
- Budulock Although Budulock isn't a program for locking down USB devices specifically, it does let you apply encrypted password security to any folder or USB port that is accessible on your computer.
- URC Access Modes A freeware alternative with limited capability that nevertheless provides enough safety to suit your demands for USB port locking for small businesses, especially those concerned about cost.
- Gilisoft USB Lock Primarily designed for small business networks because it provides a very minimal set of USB lockdown settings that only function on the device that the software is installed within.
Device Control Software
One of the best network solutions you can utilize is device control software. Any data that is sent between the devices on your network and any portable storage, such as USB flash drives, is monitored and controlled by this software. By providing a single point of management for all connections from external devices, device control software enables you to physically prohibit any undesirable USBs from your network.
You can monitor the data delivered and flag any that may be hazardous if you keep allowing flash drive connections as an alternative. You'll notice that a lot of device control solutions are included in complete DLP software packages—Data Loss Prevention (DLP) software and device control software go hand in hand.
This article discusses seven different USB lockdown software solutions that you can use to secure your network from data loss and USB-propagated malware.
Our methodology for selecting a USB lockdown tool:
We reviewed the market for USB lockdown systems and analyzed tools based on the following criteria:
- Identify your data protection and compliance requirements like GDPR, HIPAA, etc.
- Real-time alerts, device control, password protection, logging, and monitoring.
- OS compatibility and integrations, other antivirus, and firewall.
- User interface, centralized management, and customization.
- Reputed tool with robust customer support and assistance.
- Evaluate cost as per your organization's budget and licensing models to find the best fit.
- Free trial to explore detailed features.
The Best USB Lockdown Software Tools
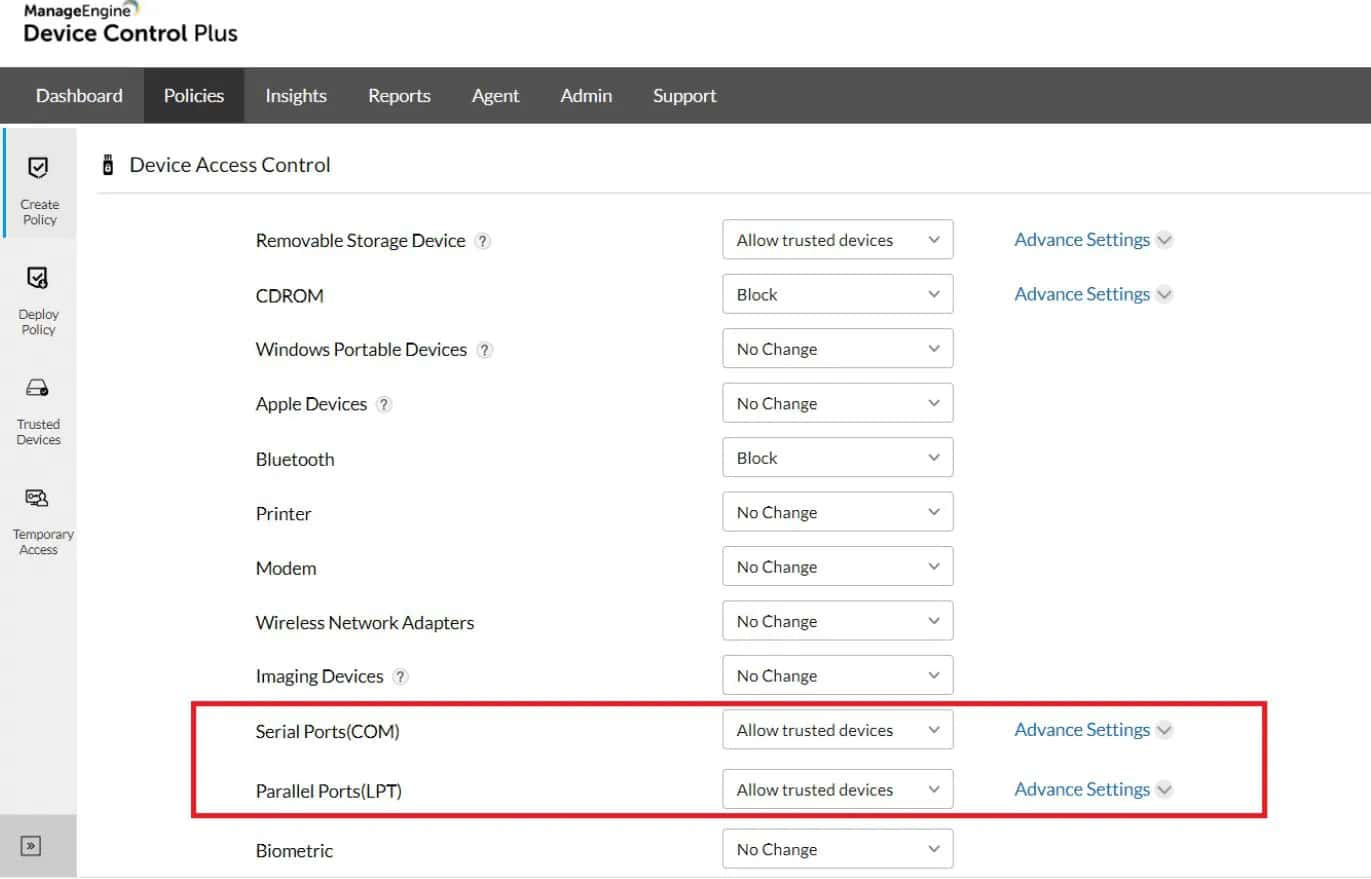
1. ManageEngine Device Control Plus – FREE TRIAL
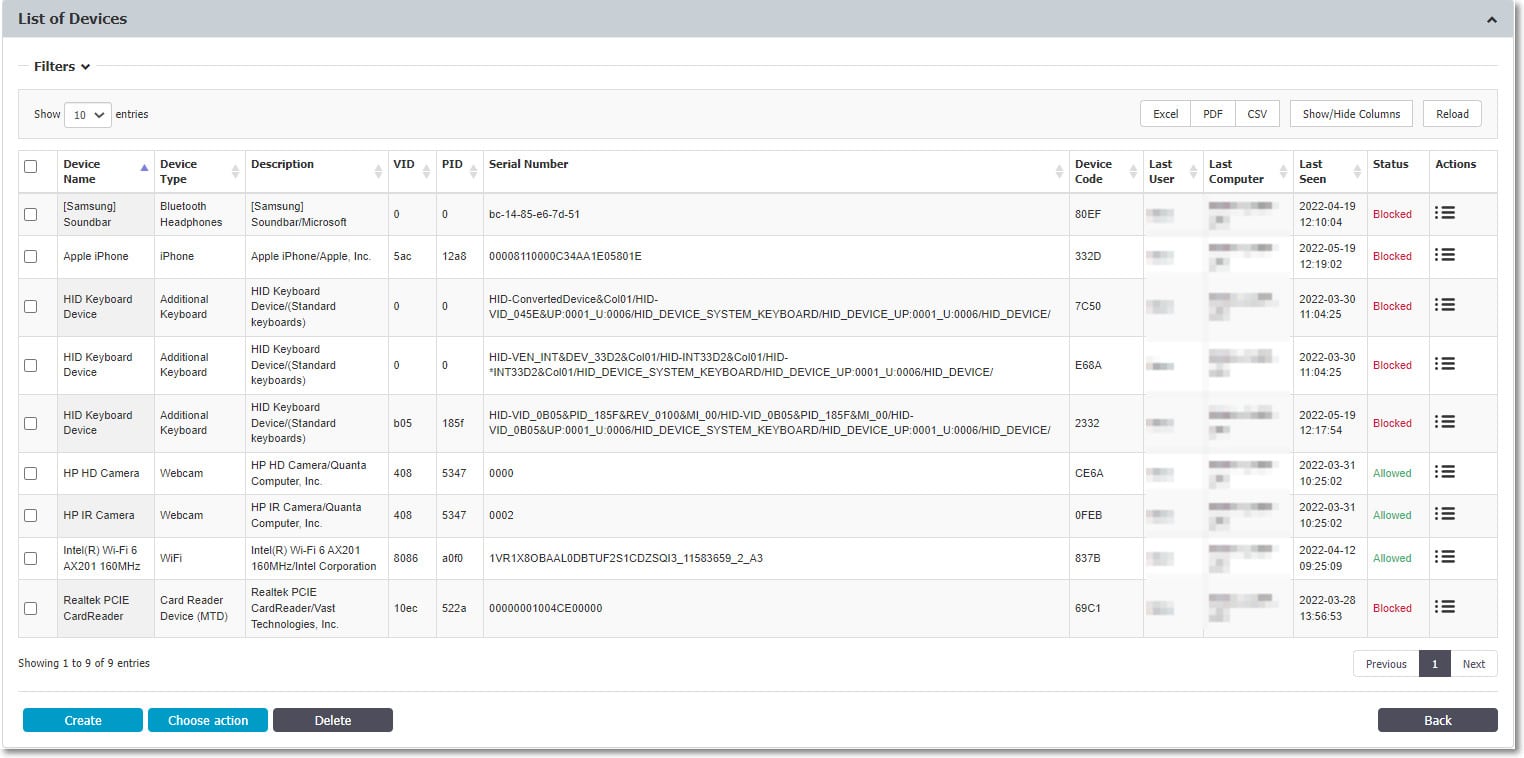
You can monitor and restrict USB access across your network with ManageEngine Device Control Plus, a comprehensive DLP software solution. Monitoring network traffic between your endpoints and USB flash drives allows you to identify harmful malware and stop it from accessing your private information. With a straightforward agent rollout and monitoring dashboard for your remote network administration requirements, the product is made with network administrators in mind. To enhance your reporting and monitoring capabilities, the solution features extensive dashboarding and data auditing systems.
Key Features:
- Real-Time Analytics Dashboard: Implements a comprehensive, real-time analytics dashboard that offers detailed insights into device usage, file transfer activities, and security incidents.
- Automated Compliance Reports: Develops automated tools for easy generation of compliance reports aligned with standards like GDPR and HIPAA, streamlining compliance efforts for businesses.
- Enhanced Mobile Device Management: Integrates advanced mobile device management capabilities to monitor, control, and secure mobile devices more effectively, particularly in a BYOD environment.
- Predictive Threat Analysis: Incorporates machine learning algorithms to predict and mitigate potential security threats based on usage patterns and anomaly detection.
Why do we recommend it?
We recommend ManageEngine Device Control Plus because it can help organizations to prevent severe cyber attacks, data leaks and other harmful threats. It comes with outstanding built-in features such as data loss protection (DLP), device and port control, file access control, and more. You can easily get started with this tool with a simple installation. We personally love its zero-trust strategy because it only allows the trusted device lists authorized by you. You can also set one-time access for particular profiles with an expiry date for particular projects.
Other capabilities allow you to give users temporary access for predetermined lengths of time, which might reduce productivity sluggishness when you need to rapidly access something that is knowingly safe but isn't fully registered.
Who is it recommended for?
If you are a high-profile organization seeking uncompromising security, this is your go-to tool. It is highly recommended for IT administrators, cyber security experts, compliance managers, and others. It provides granular control and access management of every little thing within the organization. You can be at peace because it prevents illegal data leaks and transfers, and ensures your security standards and regulations remain intact. The excellent features like real-time monitoring, audit trails, and detailed reporting to manage and secure sensitive data across all the endpoints of your network infrastructure.
Pros:
- Complete Device Management: Provides centralized management of a number of devices, increasing their reliability, and meeting security and regulatory requirements.
- Detailed Reporting: Offers strong business intelligence to observe device utilization and discuss and counter security threats.
- Easy Integration: Seamlessly integrates with existing IT environments, minimizing setup time and complexity.
- Flexible Policies: Enables the detailing of the control policies in a way that may suit the inherent organizational requirements.
Cons:
- Resource Intensive: May lead to a high demand for system resources, as they need to be utilized for this program to work efficiently without slowing down the system.
The software can be downloaded for free and used for 30 days. A year-long gateway server license costs $345. The software itself operates on a subscription model, with an annual license typically costing $595 for 100 devices.
EDITOR'S CHOICE
ManageEngine Device Control Plus is our first priority when it comes to choosing USB lockdown software to achieve a secure network. It is best at detecting unverified USB devices and controls devices and files effectively across the network. If you are an admin, you can monitor and keep an eye on the user's activities. Other than this, you can also lock specific USB ports to make them unreachable by users and prevent suspicious activity. Overall it is the best tool recommended by cyber security experts and top-notch professionals to maintain productivity, a safe and optimal environment within the organization.
Download: Download 30-Day Free Trial
Official Site: https://www.manageengine.com/device-control/usb-blocking.html
OS: Windows Server
2. Endpoint Protector
Device control is a feature of Endpoint Protector by CoSoSys that guards your network against malicious USB firmware-based attacks at each endpoint. Endpoint Protector uses data loss prevention tools to safeguard your network against data leakage in addition to safeguarding USB-propagated malware.
Key Features:
- Advanced Encryption Options: Offers multiple encryption methods for data at rest and in transit, enhancing the security of sensitive data across all platforms.
- Context-Aware Policies: Focuses on the context-aware security policies up to the network surroundings, user’s activity and the health check of devices.
- Integrated Phishing Protection: Introduces another layer of protective measures including mechanisms for the identification of phishing links and preventing their use supplemented by the DLP protocols.
- Cross-Platform Portability: Improves the portability, adaptivity and performance and at the same time, ensure that it retains the full security and functionality that is needed to run cross-platforms.
Why do we recommend it?
As the name says it all, it's the Endpoint Protector means it helps you protect all your endpoints with 100% assurance. This tool blocks, controls, and monitors the external peripheral devices connected to the network such as Bluetooth, pen drive, and other USBs to prevent data theft. It offers centralized device management with granular control. Admins can have full control on the connected storage devices and USB ports. It gives real-time reports of all endpoints based on the USB activity and you can also customize the roles and permissions to remove if anything is harmed or suspicious.
The solution is fully cross-platform and requires dispersing a single, lightweight agent over your network. A web-based interface is used to manage monitoring and settings. Even when the device is offline, you can still authorize remote USB access for brief connections. For more precise control, you can define more comprehensive rules based on policy.
Who is it recommended for?
This tool is helpful for anyone who needs to achieve robust data and USB access management. It is also useful for various sectors, such as healthcare, finance, and education, which handle sensitive information. This tool is best at preventing data breaches because of its robust data loss prevention (DLP) features, encryption, controlling device usage, and monitoring of data transfers. You can secure your sensitive data, support compliance with regulations like GDPR and HIPAA, and enhance your overall endpoint security management.
Pros:
- Cross-Platform Support: Works across multiple operating systems, providing broad protection.
- Real-Time Monitoring: Provides real-time rate control for data and shields data leakage.
- User-Friendly Interface: Boasts a well-constructed GUI that enhances the ease of modifying its data protection policies.
- Granular Control: Provides a very granular level of control over the data and its handling, including transfer and use.
Cons:
- Costly: May be relatively costly because it is a complex system with a range of features that may be helpful for small organizations.
The solution is accessible on the business website for a 30-day free trial. You must ask CoSoSys for a customized quote to learn the entire cost of the program. However, keep in mind that the price may vary greatly based on your specific needs.
3. Drivelock
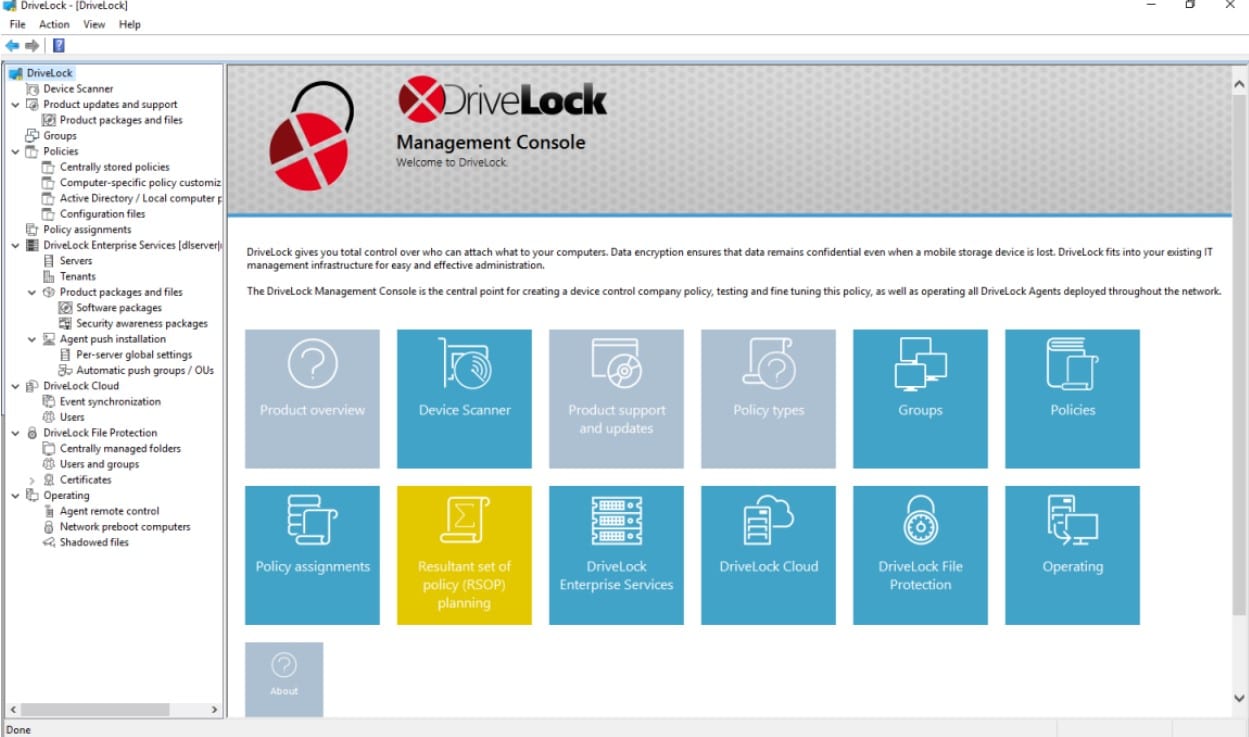
By using both the drivelock USB restrictions and the integrated encryption and antivirus system, Drivelock establishes itself by completely protecting your devices from USB-based malware attacks. Regardless of the size of your organization, this solution offers a rather straightforward collection of highly optimized functionalities that make it ideal for the task it promotes.
Key Features:
- Dynamic Data Masking: Masks data to prevent data leakage even when agreed to be accessed by other users, by modifying the data to be accessed on the fly.
- Decentralized Management Option: Decentralized approach to management console and has architecture built for the corresponding multiple control points across various geographical locations.
- Blockchain Logging: Implements blockchain technology to record all the data they interact with or transmits to other entities in an unalterable manner for improved security and audit trail of compliance.
- AI-Driven Behavior Analysis: Employ AI-driven behavior analysis to automatically adjust security policies and provide proactive protection based on evolving threats and user behavior patterns.
Why do we recommend it?
DriveLock offers superior USB locking due to its robust endpoint security and Zero-Trust principles. This tool offers additional capabilities like device encryption and application control, enhancing its utility. Its straightforward management panel will make administration easier by emphasizing important data and KPIs. IT managers can easily manage and secure USB devices and other endpoints with this user-friendly, widget-based interface that is color-coded and intuitive.
This software allows you to set security constraints for several types of external storage in addition to merely safeguarding USB flash drives. With no backdoors, and with 2FA support, encryption is incredibly safe and relatively rapid. You should also consider using the Encryption 2-Go function, which offers user-transparent encryption for external devices and data media.
Who is it recommended for?
It is especially helpful for industries that handle sensitive data often, such as healthcare, finance, and government. DriveLock's Zero-Trust methodology ensures comprehensive security in conjunction with features like USB locking, application control, and device encryption. Because of its simple administration dashboard and customisable interface, it is a great option for professionals looking for effective, user-friendly security solutions to guard against data breaches and illegal access.
- High Customizability: Highly customizable to various business environments, enhancing its effectiveness.
- Strong Encryption: Provides strong encryption methods to secure data comprehensively.
- Centralized Management: Centralizes management of security policies, making administration easier.
- Extensive Compliance Features: Supports compliance with many international security standards.
Cons:
- Complexity in Setup: Setup and configuration can be complex, requiring technical expertise.
Drivelock's software offers a free 30-day trial period during which you can evaluate its functionality. After the trial time, pricing and subscription alternatives will be available, with each client costing about $70.
4. Symantec DLP
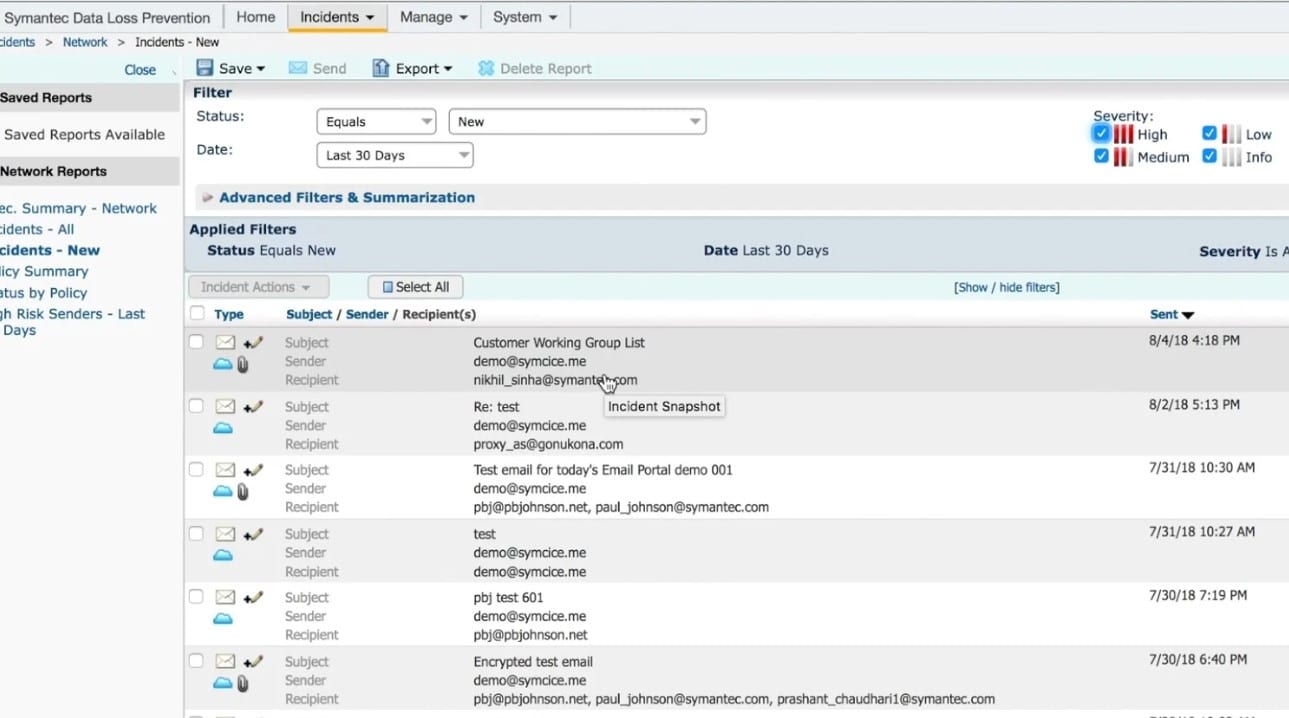
The complete Data Loss Prevention (DLP) package, Symantec DLP has capabilities for USB port lockdown as part of its feature-rich toolkit. Symantec DLP scans endpoints, network file shares, databases, and other data repositories for sensitive data to give thorough visibility and control over your information. You can find sensitive information nearly anywhere and in any file type by using content-aware detection techniques with DLP.
Key Features:
- Cloud Data Protection: Broaden DLP operational coverage for devices with options of encryption and policy for more cloud services and storage solutions.
- Integrated Incident Response: Build in an automated incident response system that can react in real-time to threats detected by the DLP system, reducing the time between detection and mitigation.
- Advanced OCR Capabilities: Enhance the functions of OCR to precisely detect and redact PII data contained in digital image formats and scanned papers in multiple languages.
- Customizable End-User Education: Automatically generate customized alerts and educational tips for end-users when a potential data breach attempt is detected, helping to improve security awareness.
Why do we recommend it?
Symantec Data Loss Prevention (DLP) is highly recommended as it offers such strong protection against both deliberate and unintentional breaches of sensitive data. It provides accurate insights into the locations of sensitive data and its movements across cloud, web, email, endpoint, and storage systems. With a common policy architecture, Symantec DLP streamlines data security and enables consistent incident detection and response for both on-premises and cloud environments.
You can also reduce the impact of your DLP efforts on end-users and get rid of false positives. The solution offers choices for data encryption and thorough compliance reporting. Large and enterprise-scale enterprises that require a more complete DLP solution, which includes USB port locking, are best suited for this solution.
Who is it recommended for?
Businesses that prioritize privacy should use Symantec Data Loss Prevention (DLP). This tool offers the best level of protection and prevents cyber attacks, compliance issues, and data breaches. It can benefit various businesses due to its extensive detection, monitoring, and protection capabilities. You can have complete visibility and control over private data, no matter where it travels, offering strong protection against data breaches and guaranteeing compliance with privacy laws.
Pros:
- Industry-Leading Technology: Known for its robust and advanced data loss prevention technology.
- Wide Range of Features: Offers a comprehensive set of features for data protection across endpoints, networks, and storage.
- Global Policy Enforcement: Enforces policies globally across an organization’s entire digital landscape.
- Strong Incident Response: Provides powerful tools for incident response and forensic analysis.
Cons:
- User Experience: The interface and management tools can be cumbersome, making it less user-friendly.
A full-year license of the enterprise edition of the product costs about $96 at MSRP and is available from several Symantec partners.
5. Budulock

While Budulock isn’t strictly a USB lockdown tool, it allows you to apply encrypted password protection to any accessible folder on your system, which extends to USB access. By adding an encrypted password barrier to your USB access, you can effectively simulate USB port locking.
Key Features:
- Multi-Factor Authentication: Introduces multi-factor authentication for accessing locked folders or USB drives, adding an additional layer of security.
- Remote Management: Enables remote management of folder and USB locks for administrators, ideal for managing work-from-home scenarios or distributed teams.
- Time-Based Locking: Implements time-based locking features where access to certain data is restricted based on the time of day or week, useful for controlling access during non-working hours.
- Audit Trails: Provides detailed audit trails that track access and attempted access to locked folders and USB drives to enhance security monitoring and compliance.
Why do we recommend it?
We recommend Budulock for its robust folder and USB flash drive protection. Budulock adds password protection to any folder on your system, including those on portable devices like USB flash drives. It prevents unauthorized USB flash drive access on your PC without the correct password, safeguarding your data from theft and infection. Budulock doesn’t disable the flash drive itself; it ensures that unauthorized drives cannot operate on your system, while your flash drives remain functional on unprotected systems.
The software itself is freeware, and extremely lightweight and straightforward to use. It has a specific purpose: applying password restrictions to folders. It executes this function extremely well by reducing unnecessary steps and focussing solely on the required functions. The Flash Drive Lock, which is the USB password lockdown feature, is the function you need for limiting USB access on your network.
Who is it recommended for?
It is especially valuable for enterprises that use portable storage devices. Budulock assists professionals by password-protecting files and preventing unwanted USB flash drive access. This ensures that data cannot be stolen or systems get infected by unapproved drives. Budulock improves data security, guards against infection, and ensures the integrity of critical information by preventing unauthorized USB use. If you are IT managers or cybersecurity specialists, then Budulock is suitable for achieving data security goals.
Pros:
- Simplicity: Non-complex tool designed for the locking of folders and USB devices.
- Lightweight: Minimal system resources on which it is run so suitable for less powerful systems.
- Effective for Personal Use: Very useful for those who want to use it and don’t have server space: mainly for individual users who want to protect their data.
- Free: Serves a significant benefit to the users who are using it privately and not commercially.
Cons:
- Limited Features: Lacks advanced features that might be necessary for enterprise environments.
Budulock is fully free to download—there are no premium features or add-ons that need to be bought. It can be acquired from several freeware sites, including the one linked above.
6. URC Access Modes
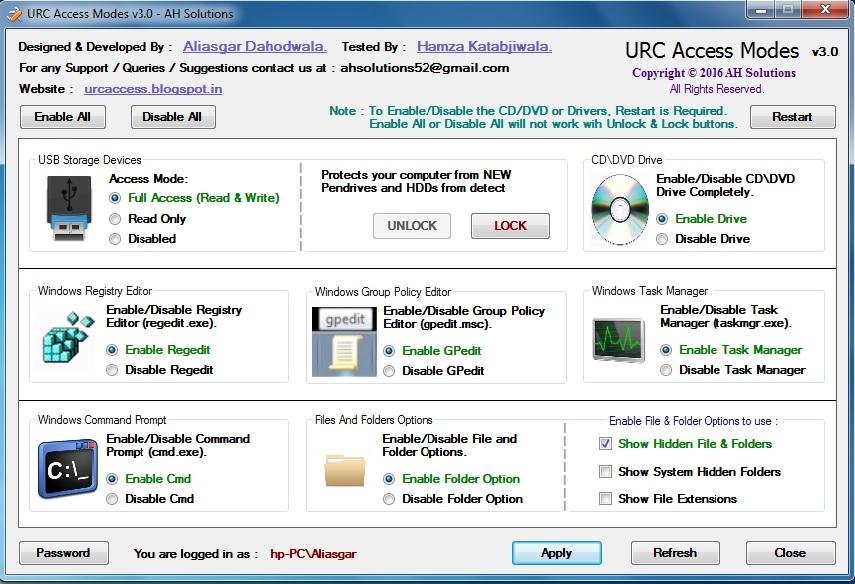
For small enterprises, especially those worried about cost, URC Access Modes is a freeware option with minimal functionality that nonetheless offers sufficient protection to meet your USB port locking needs. Only those who are unable to buy standard USB port locking solutions, or if port locking is a minor problem for your company, would we advise using this solution.
Key Features:
- Custom Access Levels: Develop a more granular access control system that allows for custom access levels depending on user roles and responsibilities.
- Integration with IoT Devices: Expand functionality to integrate with IoT devices for smarter and more secure physical access controls.
- Voice Recognition Features: Incorporate voice recognition capabilities to provide a hands-free, secure method of access control.
- Real-Time Alerts and Monitoring: Enhance the system with real-time alerts and monitoring capabilities to immediately notify administrators of any unauthorized access attempts.
Why do we recommend it?
If you are looking for a free tool for comprehensive desktop and laptop protection, you must try URC Access Modes. It has a password-protected interface, and includes various essential tools. These include a USB Tool, CD/DVD Tool, Registry Tool (regedit.exe), Command Prompt Tool, Task Manager Tool (taskmgr.exe), and much more. It prevents data theft by disabling USB mass storage devices and ensures that no unauthorized data transfer occurs. It also has dual protection and safeguards against viruses, enhancing overall system security.
Although the UI isn't up to par with more expensive software, it has port access limits as well as several additional sources that can be restricted, including CD drives, regedit, and command prompt. Keep in mind the risks associated with unrestricted USB access, and if you have personnel that frequently utilize USB media, think about investing in more comprehensive solutions.
Who is it recommended for?
If you are an IT manager, cybersecurity expert, or company owner who requires minimal control over your computer systems, you will find URC Access Modes perfect. This tool offers complete protection by blocking virus transfers, limiting data theft, and disabling unauthorized USB mass storage devices. It's free to use and ensures strong system protection and control, preserving data integrity and thwarting illegal access.
Pros:
- Flexible Access Control: Provides a rather wide list of settings regarding the access control of users.
- Integration Capabilities: Expandable to other security systems to create a stronger security setup.
- User-Specific Settings: Additional controls that make it possible to have settings defined by the user, resulting in improvements in the level of security offered.
- Audit Trails: Produces audit logs that assist in tracking access and meeting such requirements.
Cons:
- Adaptivity Issues: These may present some limitations on adaptability in larger environments or when several configurations are necessary.
There are no premium features or add-ons that must be purchased with URC Access Modes; it is entirely free to download. URC Access Modes is only available for Windows machines.
7. Gilisoft USB Lock
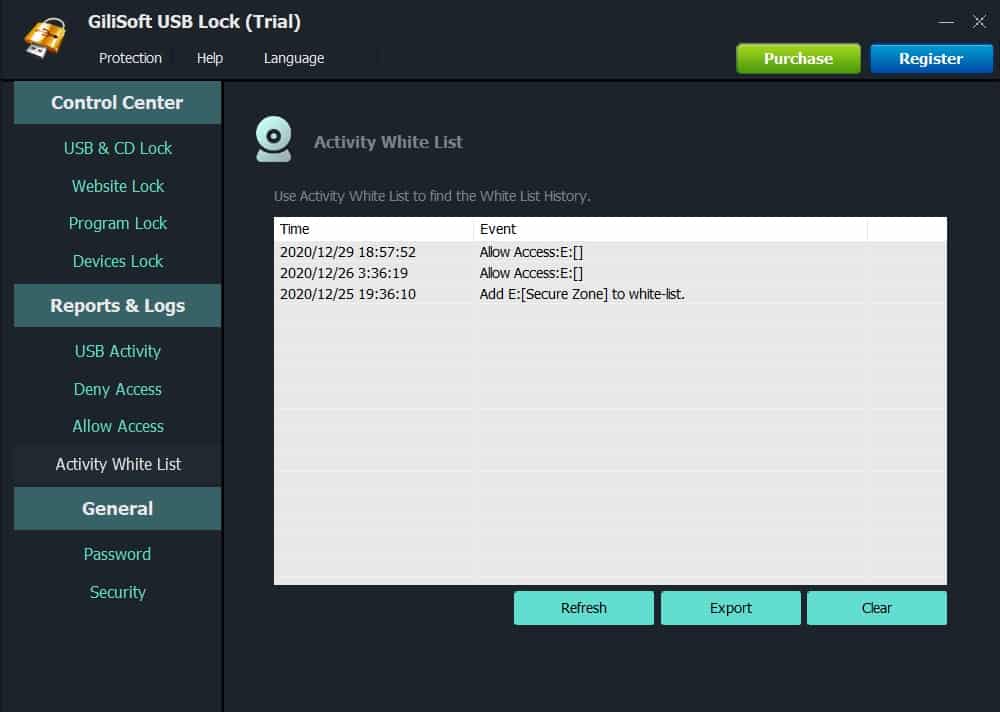
Because it offers a very basic set of port locking options that only work on the device that the software is installed within, Gilisoft USB Lock is primarily made for small business networks. This is one of the best solutions available when you only need to secure a few devices because it is simple compared to some of the other alternatives on this list, but it is also inexpensive and easy to use.
Key Features:
- Endpoint Anomaly Detection: Checks out unusual activities of devices that are a potential threat to the security of a given system.
- VPN Enforcement: Provides an alert, with the option to force the user to use a VPN connection, when connecting to certain high-risk USB devices or when copying potentially threatening files.
- Enhanced Compatibility: Updates compatibility to support newer USB standards and devices, ensuring the tool remains effective with evolving technology.
- User Behavior Analytics: Monitors and evaluates user actions continuously, helping to preemptively resolve potential security risks before they escalate.
Why do we recommend it?
If you need heavy protection for USB devices then we highly recommend DriveLock for robust USB locking needs as it effectively prevents data leaks and unauthorized data copying to USB drives, including Android/iPhone devices. This tool will block the use of external drives (CD/DVD), and other portable devices, to maintain the integrity of the business and deliver comprehensive protection. You can also restrict the use of mobile hotspots via USB, enhancing security. DriveLock allows you to confidently share your PC without fear of data theft, making it an essential tool for preventing data breaches and unauthorized access.
It offers just personal protection and lacks centralized control features, but it may be distributed over a network using a command-line and pre-configured parameters. For compliance reasons, you can set reporting logs and completely deny access to illegitimate USB devices.
Who is it recommended for?
For those in charge of data security, IT administration, and business ownership who must safeguard confidential information from theft or illegal access, GiliSoft USB Lock is the perfect solution. Organizations in industries where data security is crucial, such as finance, healthcare, and law, will especially benefit from it. By avoiding data theft and unlawful copying, GiliSoft USB Lock benefits enterprises by restricting unauthorized USB drives, external devices, and CDs/DVDs. In addition to preserving data integrity and adhering to security laws, this guarantees the protection of sensitive information.
Pros:
- USB Protection Focus: Specifically developed to offer robust security to the USB and ensure safety from any form of unauthorized use of the USB.
- Broad Compatibility: Supports different versions of Windows, thus making it to be more versatile to fit different environments.
- Password Protection: Password protection features that have been added as a measure of security.
- Ease of Use: Not difficult to operate, and can be used by anyone without too much technological experience.
Cons:
- Limited to Windows: Primarily available only for Windows users, limiting its use in mixed or non-Windows environments.
A full trial can be downloaded from the website, which is ideal for feature testing. The whole program is reasonably priced for small company use, costing roughly $50 for a lifetime license on a single machine.
In Summary
There is a large variety of options available for locking down USB access on your network, though most premium solutions are rarely developed for strictly that purpose. While there are several freeware USB lockdown software solutions available, it is considered a simple feature and only comes as part of a wider toolset in enterprise or large-scale corporate products.
This means that if you need an enterprise-level solution, but only need the USB lockdown functionality, you might end up having to pay for an expensive feature-rich product for only one fraction of the product's capabilities—the best option available to you in this circumstance is probably Drivelock.
Alternatively, if you are on a smaller network and just need an easy-to-distribute solution that just does the job, then you can select from the three presented cheaper options. Gilisoft USB Lock has a few extra functions presented in a cleaner package compared to URC Access Modes, but they effectively achieve the same thing.
If you’re looking for a more comprehensive solution that comes as a fully-featured DLP solution, then Symantec DLP, ManageEngine Device Control Plus, and Endpoint Protector by CoSoSys are worth your consideration. Each of them can perfect USB lockdown, but all of them have different other features that are worth checking through before making your purchase commitments. ManageEngine Device Control Plus and Endpoint Protector by CoSoSys sit higher on this list purely because they have trials available that make them infinitely more accessible than Symantec DLP.